Sustainability
Information Security and Personal Information Protection
Our Approach and Governance for Information Security and Personal Information Protection
We are committed to the appropriate management of information assets, including our customers’ personal information, based on our Information Security Basic Policy.
In accordance with our Personal Information Protection Policy, we clarify the usage, acquisition, management posture, and methods related to personal information handling. We also strive to thoroughly inform each of our employees and enhance the proper protection and management of personal information.
We report information on these Policies such as initiatives and a progress state regularly to the Comprehensive Risk Management Committee, the Executive Management Meeting and the Board of Directors.
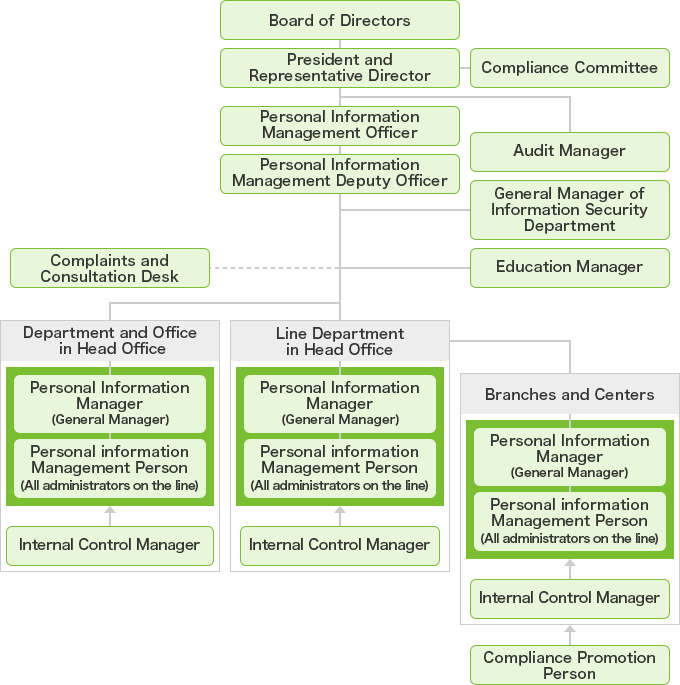
Personal Information Protection and Management System
Under the guidance of our Personal Information Management Officer, delegated by our President and Director, we conduct comprehensive control and management of personal information based on relevant laws and internal regulations to ensure its proper handling.
Organization structure
Acquisition of Security Certifications
Currently (as of June 2025), we have obtained the following security certificates.
| Certification Name | Certified Range | Certification Year |
|---|---|---|
| Privacy Mark | Entire Company | 2006 |
| PCIDSS | Authorization System System for authorizing credit cards and loan cards (approving card uses) |
2011 |
| Web-based Systems Systems for providing one-stop services such as application procedures and access to card statements to customers who use services such as credit cards and individual credit. |
2013 | |
| Mission Critical Systems Critical systems for conducting a series of operations from receipt of applications to tabulations and managing information on customers, contracts, member stores and alliance partners |
2018 | |
| Data Transfer and Exchange Systems Systems for transferring and exchanging data from/to member stores and alliance partners |
2020 | |
| Information-based System Business Intelligence system based on mission critical systems |
2024 | |
| ISMS | Operations Center in Fukuoka (Card Issuance Operations) | 2018 |
| All Operations Centers (Card Issuance Operations) | 2021 |
Information Security and Personal Information Protection Initiatives
1.Strengthening System Security Measures
Our company is continuously working to enhance system security measures. We analyze from perspectives of the level of attack techniques and whether the source of the attack is internal or external, and prioritize accordingly.
1)Measures Against Unauthorized Data Extraction from Within
- Restrict data export functions from internal computers and prohibit connections to USB memories and smartphones.
- Limit access to websites that could lead to information leaks.
- Enforce user rights control and compliance with password policies to regulate system access.
2)Measures Against External Attacks
- 24/7 monitoring of networks and devices for early detection and immediate response to incidents.
- Establishment of a multi-layered defense system, including measures against unauthorized intrusions and malware.
- Implementation of regular targeted email training and e-learning to improve security literacy of employees.
2.Orico CSIRT
In response to increasingly sophisticated and complex cyber attacks and other incidents, our company has formed a security incident response team "Orico CSIRT" and implemented the following initiatives.
- 1) Immediate response to information security incidents occurring in our information system.
- 2) Quality management and improvement of security, including risk management and implementation of security measures for information system assets.
- 3) Cyber attack training status (2022 fiscal year)
-
Cyber attack training: Twice
-
3.Utilization of External Security Consultation Companies
Our company utilizes external security consulting companies to perform professional and objective evaluations of the appropriateness of our security measures and to strengthen our security measures.
4.Personal Information Protection Training
Through the following training programs for all executives and employees of the Group, including part-time workers, casual workers and temporary employees, we strive to thoroughly inform and implement the protection of personal information.
- 1) Company-wide e-training (once a year)
- 2) Departmental, office, and branch unit-based training on safe management of personal information (all year round)
- 3) Personal information handling officers: 3,491 (as of March 2025)